In the past I’ve written a blog on how you can pre-configure authentication methods for end users either manually or via the Microsoft Graph API. These authentication methods are used by Azure Multi-Factor Authentication or Self-service Password Reset within the Azure AD by end users.
Based on the developments from Microsoft and requests I got from the community I’ve created a new PowerShell script which is based on the Microsoft.Graph module and is able to do updates in bulk for your end users in a simple way. This can be very helpful if administrators need to import data into Azure Multi-Factor Authentication from their previous SMS multi-factor authentication solution.
The script can Add, Update or Delete the following Authentication Methods:
- Mobile Phone.
- Alternate Mobile Phone.
- Office Phone.
As you may already know I always prefer to use the Authenticator App to be used with Azure Multi-Factor Authentication as in the end that’s safer and one of the ways to move to a password-less world. So, if you’re going to implement phone numbers as Multi-Factor Authentication methods for your end users, please have a look at the Authenticator App Nudge blog as well which I’ve written so you can later on prompt your users to move multi-factor authentication from voice/SMS to the Authenticator App!
Using the Microsoft.Graph PowerShell Module to bulk update authentication methods.
Now if you need to do bulk updates or want to build your own process around provisioning of Azure Multi-Factor Authentication methods within the Azure AD, I would strongly recommend you to use the Microsoft.Graph module which is based on the Microsoft Graph.
Biggest advantage of using the Microsoft.Graph module is that you can automate actions via PowerShell. Meaning you can write a PowerShell script which connects to the Graph API to change authentication method values on user accounts.
To get this working we first need to create a service principal, don’t know how you need to create one? Don’t worry, I’ve written another blog which explains this in a step-by-step scenario which you can find here.
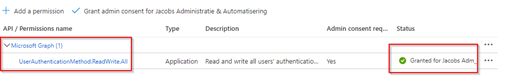
The only difference compared to that blog is that we do need to configure the service principal with different permissions, the only permissions which is required is UserAuthenticationMethod.ReadWrite.All, based on the Application type, based on the Microsoft Graph API and need to be consented (as can all be seen below).
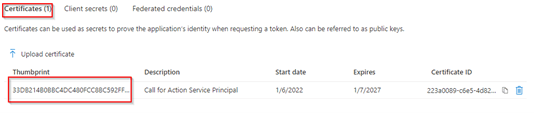
Furthermore, by using this example, the Service Principal must make use of a certificate, therefore make sure a certificate is added and you’ve noted down the value of the certificate thumbprint and besides have your TenantID and ApplicationID (of the created service principal) noted down as well.
We’re now ready to use the PowerShell script I’ve written (and which you can customize on your own), which can use this Service Principal to talk to with the Microsoft.Graph module to the Microsoft Graph API. This to Add, Update or Delete Authentication methods. The script uses an input file which can be found here. Download them both and save them on the device where you are going to run the script.
Now let’s see how you can use the script and to understand what the script actually does, let’s just run it for one single user. Therefore, make sure the CSV file is filled with the right details.
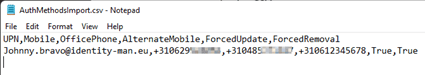
Now the file is ready, open the Pre-ConfigureAuthMethods.ps1 and make sure to configure the ClientID, TenantID and CertificateThumbprint to the values we noted above (and make sure that the machine you’re running the script with, has the certificate installed in the user store).

NOTE: In case you don’t want to use a service principal, comment line 5-7 and uncomment line 9-11. That will give you an interactive prompt so you can execute these changes based on your regular admin account.
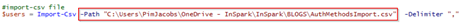
Next, make sure to change the input location of the CSV file you have just edited to point to the right location.
Once the file is ready and saved, open a PowerShell in elevated mode and run the PowerShell Script.
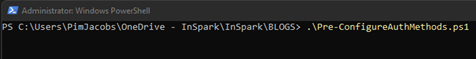
As you can see it’s updating all values (except for the Mobile method as that’s currently the default method for this end user).

If we put in multiple lines in the CSV and re-run the script we can see that it’s now updating multiple user accounts in one go (bulk).
Happy scripting and bulk updating authentication methods for your users! 🙂
When using the script, please know that:
- The script will add, update or remove authentication methods for mobile phone, alternate mobile phone and office phone for users.
- The script won’t be able to remove or update a method which is set as default for an end user.
- The script won’t be able to add or update the alternate mobile method without a mobile method configured.
- If you don’t want to use alternate mobile or the office phone value, just leave them empty in the CSV.
- If you don’t want to update or remove values for users (ForcedUpdate / ForcedRemoval), put both statements (or just one of them) to false in the CSV input file.
- If the user is enabled for SMS Sign-in as an authentication method the mobile number is by default enabled for SMS Sign-in.
- If SMS Sign-in is enabled, be aware that mobile numbers must be unique within a tenant to use the script (can’t be used twice).
- In case you don’t want to use a service principal, comment line 5-7 and uncomment line 9-11. That will give you an interactive prompt so you can execute these changes based on your regular admin account.
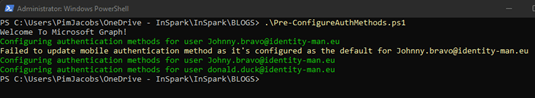
If you afterwards would check the UI within the Azure Active Directory, this would also show the value you just configured on the user account. This can be seen under the ‘Authentication Methods’ blade in the Azure Active Directory when looking at a user account (in this example Donald Duck).
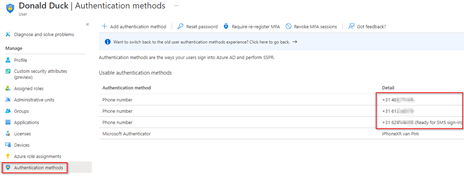
When opening the ‘Audit Logs’ for this user in the ‘Azure Active Directory’ you can see that Authentication Methods for the donald.duck@identity-man.eu user object have been updated.
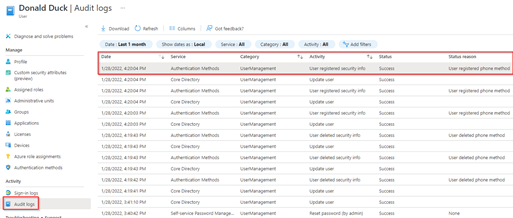
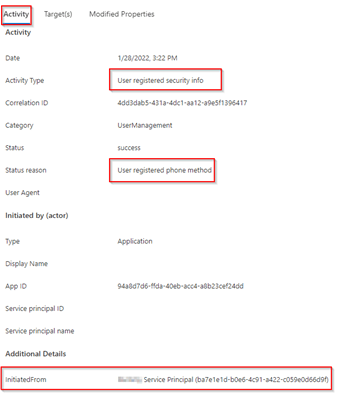
Looking at the details of the ‘Audit Log event’, which is marked above, I can see in the ‘Activity’ tab that security info has been registered for this account via the service principal I created earlier.
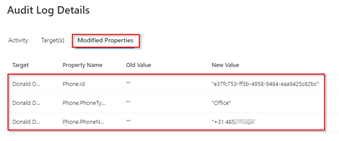
Looking at the ‘Modified Properties’ tab you can see what is actually changed for the user. In this example it’s the Office Phone value which now has been configured with a number and added beneath the account.
So no worries, everything you’re with the script can still be tied together :-).
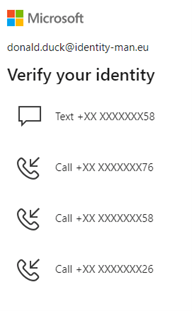
Once you now try to logon to https://myaccount.microsoft.com with the account for which you just configured the authentication methods and the account is matching a multi-factor authentication conditional access policy, you can see that the options we put into the Azure AD can automatically be used with SMS or Voice multi-factor authentication without the user needing to enroll itself.
Conclusion
Now you’ve read all of the above you know how you can do bulk authentication method updates for your end users. All with the result that end users don’t need to walk through the Azure MFA registration process themselves.
Especially during these times (COVID-19) when we mostly work remotely being able to provision (which in some scenarios you can only do from the office) or reset authentication methods for your end users can become quite helpful.
I hope you enjoyed reading my blog and are able to re-use my PowerShell script so you’re able to provision multi-factor authentication settings for your end users via the Microsoft.Graph PowerShell Module. And don’t forget to turn on the Registration Campaign functionality to guide your users to a more safe Multi-Factor authentication method.
Stay safe and be tuned for more blogs and hope to see you again soon!
Thank you very much for this. Super helpful. Is there any way to also add alternate email address as well to this? Thanks again!
LikeLike
Hi Daniel,
Yes there are ways to do this, it’s currently not included in this script but if you’re able to code a bit you can easily edit my script and add an extra option :-).
The details for the Graph calls for email are explained here:
https://docs.microsoft.com/en-us/graph/api/emailauthenticationmethod-get?view=graph-rest-beta&tabs=http
Pim
LikeLike
Hi
Thanks for a great blog on this feature.
We wish to enable this for both existing and new users through a service now workflow.
My question is If we have user mobile phone details synced from AD to Azure via AAD connect and have already populated in the profile of a user the required field in Azure AD (mobile phone), is there a way you can interrogate the Microsoft Graph and populate that same value in the required authentication methods?
LikeLike
Hi,
No not by default, you could however create a script (in Azure Automation) which reads the value from the mobile phone field and configures that as the mobile authentication method for users (or maybe the alternate mobile phone value so users are able to still configure mobile theirselves).
The script could be targetted to run each day so it will work for existing and new accounts.
LikeLike