In this blog series I will explain to you what password-less is, why you should implement it, what options currently are available and which changes are required to make sure password-less is functioning as expected.
Organizations around the world see the beginning of a new era, where passwords are considered as a relic of the past. The costs now outweigh the benefits of using passwords, which increasingly become predictable and leave users vulnerable to digital identity theft. Even the strongest passwords are easily phishable. The motives to eliminate authentication systems using passwords are endlessly compelling and all too familiar to every enterprise IT organization.
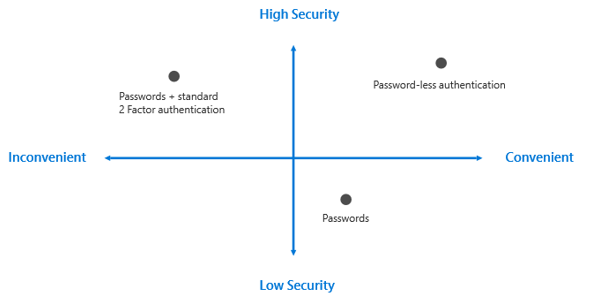
Today, IT security is moving towards password less authentication using advanced technologies like biometrics, PIN, and public/private key cryptography. Plus, new standards like Web Authentication API (WebAuthN) and Fast Identity Online (FIDO2) are enabling password less authentication across platforms. These standards are designed to replace passwords with biometrics and devices that employees already use, such as smartphones, biometrics (facial recognition or fingerprint reader) or security keys.
Password-less Strategy
Over the past few years, Microsoft has continued their commitment to enabling a world without passwords. At Ignite 2017, Microsoft shared a four-step approach which helps organizations going password-less.
- Develop a password replacement offering
- Reduce user-visible password surface area
- Transition into a password-less deployment
- Eliminate passwords from the identity directory
Going password-less is a long-term approach for secure authentication, and it’s still evolving. It can take time to transition. For users that can’t go password-less, turn on MFA to validate users and minimize prompts based on the risk of the sign-in with conditional access capabilities.
Password-less options within the Azure AD
With biometrics on mobile phones and computers becoming more ubiquitous, the number of password replacement technologies has increased.

Microsoft offers solutions based on platform, hardware, or software that you can try out today and map with your password-less authentication requirements. Introduced by Microsoft in Windows 10, Windows Hello uses biometric sensors or a PIN to verify a user’s identity. The Microsoft Authenticator app is a software token that allows users to verify their identity with a built-in biometric or a PIN when signing into their work or personal accounts from a mobile phone.
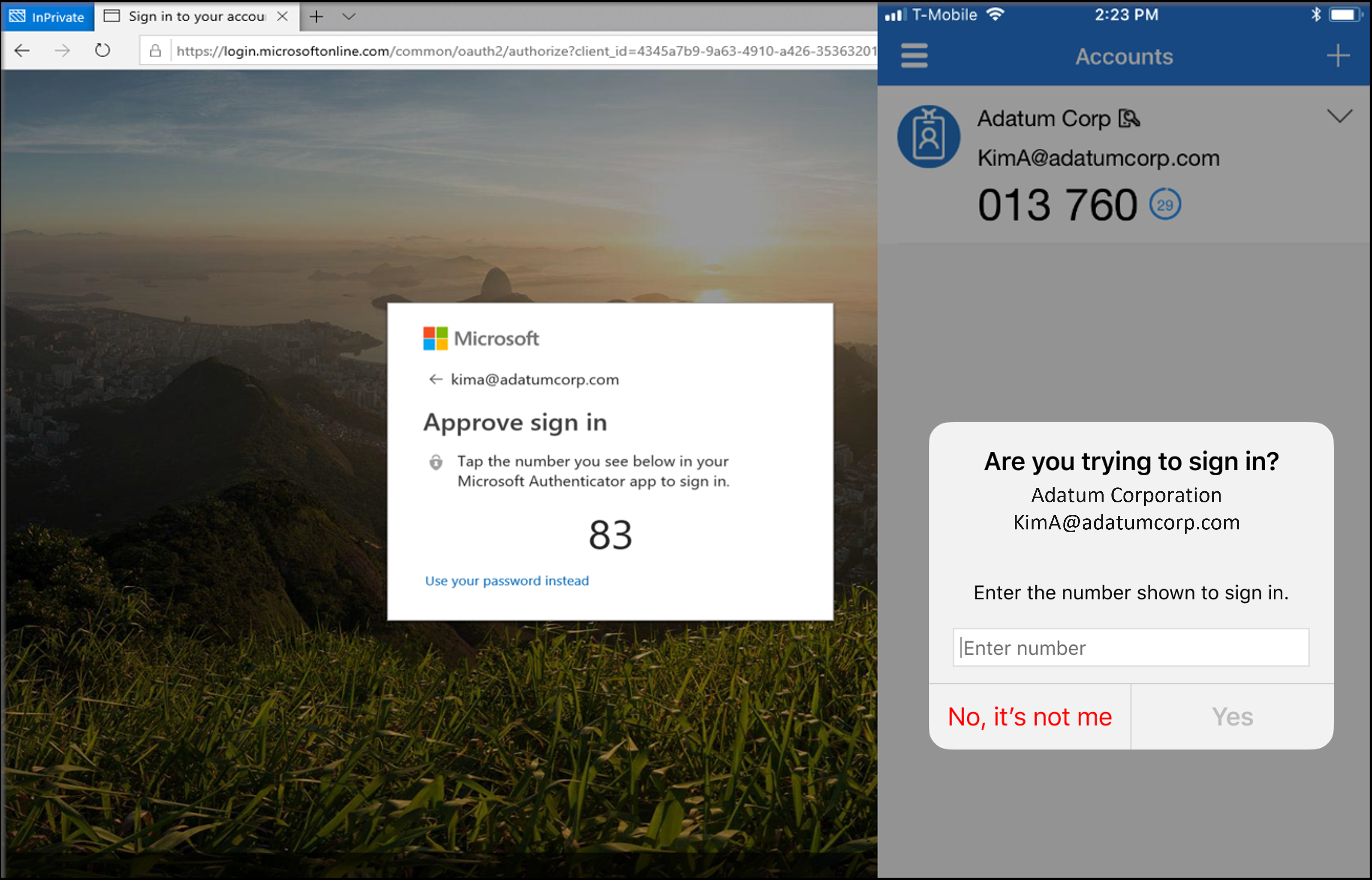
1. Password-less phone sign-in
The Microsoft Authenticator app enables users to verify their identity and authenticate to their work or personal account. Microsoft Authenticator can be used to augment a password with a one-time passcode or push notification. The app can also be used to verify multiple factors and replace the need for a password.
Instead of using a password, users confirm their identity using your mobile phone through fingerprint scan, facial or iris recognition, or PIN. Built on secure technology similar to what Windows Hello uses, this tool is packaged into a simple app on a mobile device making it a convenient option for users. The Microsoft Authenticator app is available for Android and iOS.
2. Windows Hello for Business (hybrid)
Windows Hello for Business replaces passwords with strong multi-factor authentication on Windows 10 platforms, including PCs and mobile devices. This authentication consists of a new type of user credential that’s linked to a device and uses a biometric or PIN. It lets you sign in with your face, iris scan, fingerprint, or a PIN, and enables you to authenticate to enterprise applications, content, and resources without a password being stored on your device or in a network at all. The biometric data is only used locally and never leaves the device.
Important to know is that you can run Windows Hello for Business also in a hybrid scenario. This means that an Azure AD Joined or hybrid azure ad joined device can authenticate with Windows Hello for Business credentials to your on-premises Active Directory resources. This will improve adoption and prevent a lot of authentication prompts and therefore frustration with end users.

3. FIDO2 Security Keys
FIDO2 is an evolution of the U2F open authentication standard based on public key cryptography using hardware devices. This standard is intended to solve multiple user scenarios including strong first factor (password-less) and multi-factor authentication. With these new capabilities, a security key can entirely replace weak static username/password credentials with strong hardware-backed public/private-key credentials.
These credentials cannot be reused, replayed, or shared across services. Devices and tokens that adhere to FIDO2, WebAuthN, and CTAP (Client to Authentication Protocol) protocols bring about a cross-platform solution of strong authentication without using passwords. Microsoft partners are working on a variety of security key form factors, such as USB security keys and NFC-enabled smart cards

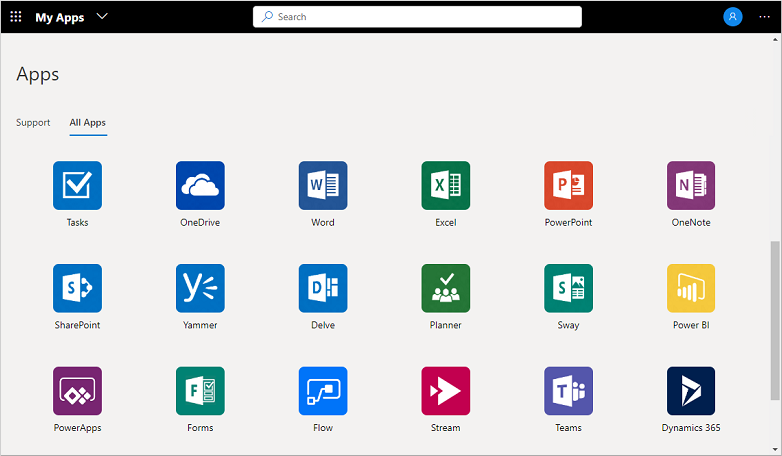
4. Enabling password-less for other apps as well
The above three options describe password-less authentication against the Azure AD or Windows 10 which is step 1 in enabling password-less. However what about all the other applications which resides within your environment like Salesforce, SAP, TopDesk or any other app you may have?
Well it’s simple if those apps fall beneath one of the types described below I strongly encourage you to connect those apps to the Azure AD:
- Azure AD Gallery applications – Azure AD has a gallery that contains thousands of applications that have been pre-integrated for single sign-on and password-less with the Azure AD. Some of the applications which your organization uses are probably in the gallery.
- Non-Gallery applications – Connected your own applications to the Azure AD, to support single sign-on and therefore password-less. You can integrate any web link you want, or any application that renders a username and password field which supports SAML, OpenID Connect protocols, or supports SCIM.
- On-premises applications with Application Proxy – With Azure AD Application Proxy, you can integrate your on-premises web apps with Azure AD to support single sign-on and password-less. This way end users can access your on-premises web apps in the same way they access services connected to the Azure AD like Office 365.
- Custom-developed applications – When building your own line-of-business applications, you can integrate them with Azure AD to support single sign-on and password-less. This can be done by registering the application with Azure AD.
Once the apps are connected with the Azure they will show up (if configured) within the MyApps portal, this will give the end user one entry point for all applications.
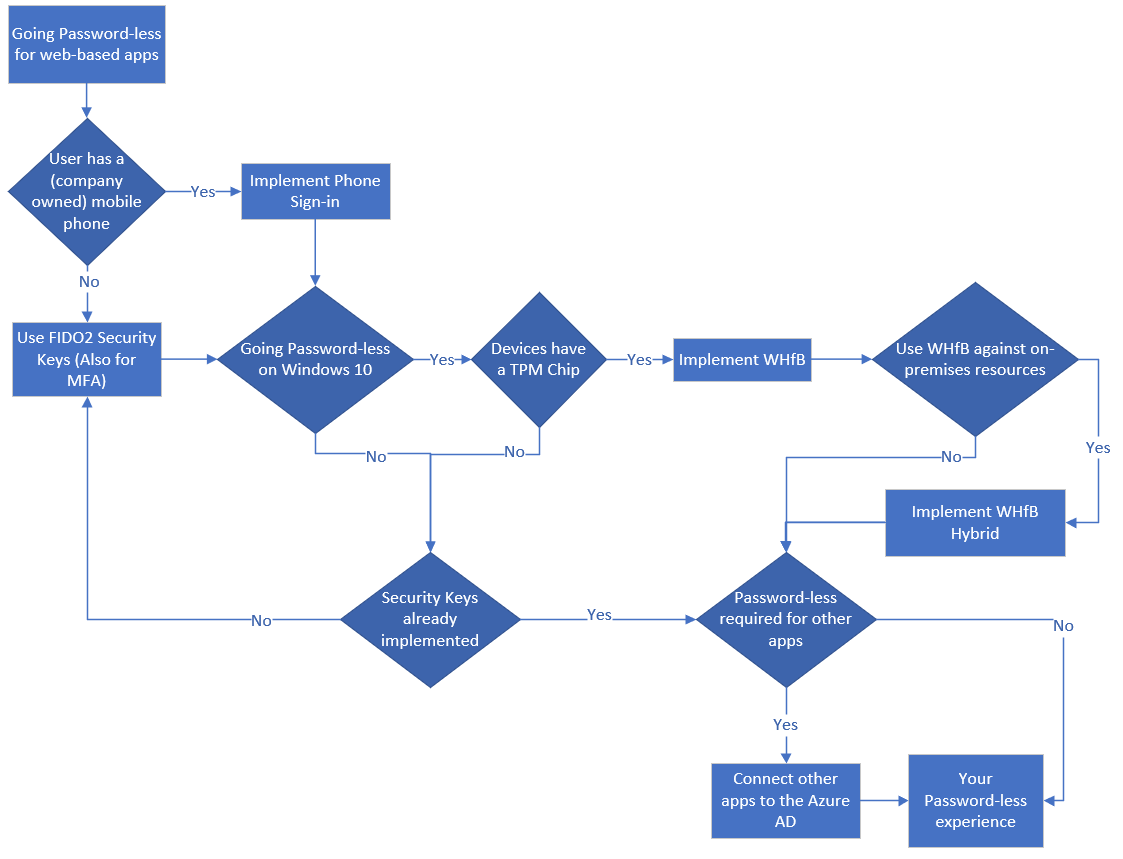
Define the strategy for your company and choosing the right technology for your environment
It’s important to find out which technology you want to use, and for that make the necessary changes. The flowchart below can help you make the right decisions and give some guideline in how to start with your password-less journey.
I hope you enjoined reading this introduction blog to password-less and I’ve encouraged you to start your password-less journey.
In the next five blogs I will explain how to implement each option separately from a technical and user point of view, once available the links below will become active:
- Introduction to a password-less era!
- Password-less 1 of 5: Going password-less with phone sign-in
- Password-less 2 of 5: Going password-less with Windows Hello for Business
- Password-less 3 of 5: Going password-less with Windows Hello for Business Hybrid
- Password-less 4 of 5: Going password-less with FIDO2 Security Keys Part 1
- Password-less 4 of 5: Going password-less with FIDO2 Security Keys Part 2
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 1
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 2
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 3
- Password-less continued: Upgrading your password-less experience with Windows Hello for Business Hybrid cloud-trust.
- Password-less continued: Using the Passwordless Phone Sign-in experience for multiple accounts on iOS!
- Password-less continued: Using a Temporary Access Pass for Bootstrapping your Passwordless Journey