This blog post is all about the Passwordless phone sign-in experience for multiple accounts on the same device. Previously by enabling Passwordless phone sign-in within the Authenticator App the functionality was limited to only one single account per device. Well good news for all iOS users, the support for multiple Passwordless phone sign-in accounts on a single device went public preview about 2 weeks ago! Want to know how to enable this for you, please keep on reading!
NOTE: If you’re an Android user, you have to be patient as this functionality is today only released for the Microsoft Authenticator App on iOS. I promise I will post another blog once Android is there as well!

Now let’s have a look at the requirements and steps we need to take to get this working smoothly!
How to get this enabled for your tenant?
First make sure you can make use of the Passwordless Phone Sign-in functionality in your tenant, therefore please follow my other blog post first to make sure all configuration items are in place.
Once you’ve made sure you configured your tenant correctly, let’s verify / prepare the settings on your mobile device to make use of multiple Passwordless Phone Sign-in accounts on a single device!
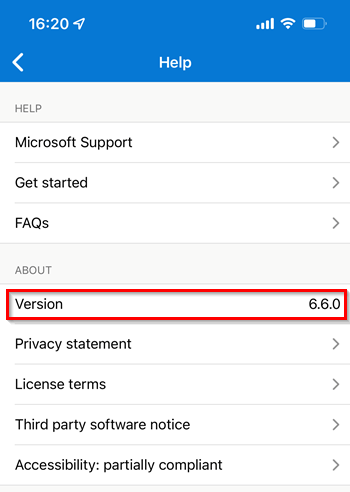
For that first of all it’s important you’ve the latest Authenticator App version (currently 6.6.0) installed and are running iOS 12.0 or later.
At second it’s important to enable ‘Usage Data‘ within the Microsoft Authenticator App to be shared with Microsoft. Important here to know is that the plan is to remove this requirement for general availability, until that time this setting needs to be enabled to use the public preview!

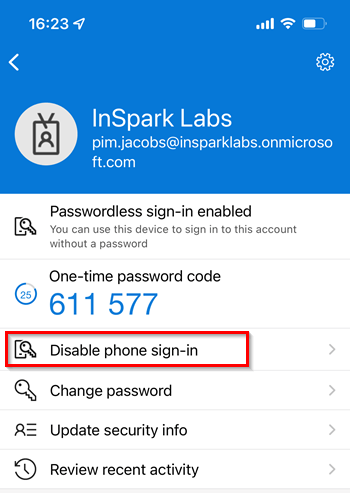
Now this has been verified and checked, please fully close the Microsoft Authenticator App and start it again and select an account which hasn’t been enabled with Passwordless Phone Sign-in and hit ‘Enable phone sign-in‘.

Now complete the sign-in process and hit ‘Register‘ to register this device to another tenant (yes another tenant as in my case it was already registered to two other tenants).
NOTE: This doesn’t mean the device get’s managed, it’s just a simple device registration within the Azure AD Tenant.

As we can see the account has now been enabled with the Passwordless Phone Sign-in experience! With the next sign-in you can now make use of the epic functionality for this particular and other accounts on a single iOS device (as long as the tenant settings are correctly configured according to this blog post and already mentioned earlier).
If you are desperate and really want to know to which tenants your device has been registered, this can easily be checked from within the Authenticator App. This can be found underneath Settings and going to ‘Device Registration‘.
NOTE: You can even unregister the device from here by selecting the tenant and hitting ‘Unregister device‘, this will of course break the Passwordless phone sign-in experience.

Conclusion
This new functionality enables the use of Passwordless Phone Sign-in for multiple accounts on a single device. So if you’re a consultant working for more companies, if you’re an administrator and have two accounts or any other kind of scenario which previously couldn’t be fulfilled with a single device, can now work! This brings in a better unified user experience as you’ve seen but also a better security level and with that you’re prepared for the future ;-).
Let’s hope Microsoft soon releases support for the Authenticator App on Android as well, as that’s still the biggest limitation factor for a big roll-out of this functionality to all users!
I again hope you enjoined reading this blog post, in my next blog as a follow-up on the password-less series I will explain to you how you can make use of a password-less enrolment via a temporary access pass for your end users (literally sign-in without a password), so stay tuned for more password-less love!
Other related password-less blogs:
- Introduction to a password-less era
- Password-less 1 of 5: Going password-less with phone sign-in
- Password-less 2 of 5: Going password-less with Windows Hello for Business
- Password-less 3 of 5: Going password-less with Windows Hello for Business Hybrid
- Password-less 4 of 5: Going password-less with FIDO2 Security Keys Part 1
- Password-less 4 of 5: Going password-less with FIDO2 Security Keys Part 2
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 1
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 2
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 3
- Password-less continued: Upgrading your password-less experience with Windows Hello for Business Hybrid cloud-trust.
- Password-less continued: Using the Passwordless Phone Sign-in experience for multiple accounts on iOS!
- Password-less continued: Using a Temporary Access Pass for Bootstrapping your Passwordless Journey
Thanks, great writeup. Looking forward to this being enabled on Android.
LikeLike
Great article! Do you have any insights on support for phone sign-in for multiple accounts on Android?
LikeLike
Hi Mike, unfortunately nothing to share yet :-(.
LikeLike