Welcome to another blog in the going passwordless series! In my last blog I’ve written about Entra ID Authentication Strengths feature and how this feature helps you to require passwordless for your end users. The Authentication Strengths feature however isn’t applied during the Windows sign-in as also mentioned within the conclusion of that blog. This blog will explain how you can easily hide the password option from the login screen in Windows 11 and make sure to require your users to work passwordless during the Windows Sign-in as well (this without removing the password credential provider)!

Having said that, let’s start with some background information. In the past a lot of blogs / articles are written by other active community members (like the ones from Peter van der Woude & Ronny de Jong) on how to remove the password credential provider from your system. All with the intention to create a fully passwordless behavior. However, fully removing the password credential provider from your system has a big impact as they explained as well, this as the password credential is, as example, used in ‘Remote Desktop Connections’ & ‘Run as different user’ as well. This means that with removing the password credential provider from your system the above-mentioned functionalities can’t make use any more of a username and password combination.
Especially for people like me, who want to work passwordless but sometimes need to connect to servers of customers which only supports a username and password combination, removing the password credential provider simply isn’t an option.
Luckily with this new feature called ‘Enable passwordless experience’ we are taking a big step into the right direction (which is released in Windows Insider build 23506). This as the ‘Enable Passwordless experience’ feature only hides the password option from the sign-in or lock screen and doesn’t fully remove the password credential provider. Therefore, functions like ‘Remote Desktop Connections’ or ‘Run as different user’ will still accept a username and password combination when the ‘Enable passwordless experience’ feature is turned on.
As with all features, there are a few important things to know about the ‘Enable passwordless Experience’ feature:
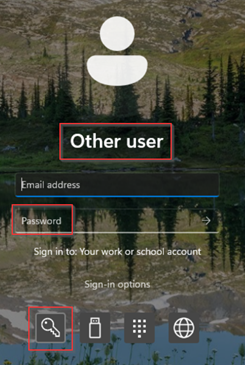
- The feature will hide the password option from the sign-in, lock screen and the account settings page. However, when selecting the ‘other user’ tile to login to your machine you can still enter your username and password as a ‘gateway of last resort’.
- It’s highly recommended to enable the web sign-in experience as well with this feature to make sure that when users forgot their PIN, lost their Security Key or get a locks screen during the bootstrap process they are still able to complete their sign-in via Web Sign-in.
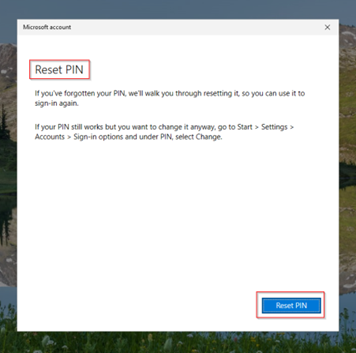
- It’s highly recommended to enable the Microsoft PIN reset service so users in your organization can change their PIN from the lock screen as well (in case they forgot their PIN). By default, this service isn’t enabled.
Now you’re up to speed with the ‘Enable Passwordless Experience’ feature, let’s start using this amazing feature, this so we can hide the password option for end users on the Windows 11 sign-in screen and make sure there are enough fallback methods available.
Step 1 – Enable the Microsoft PIN reset service
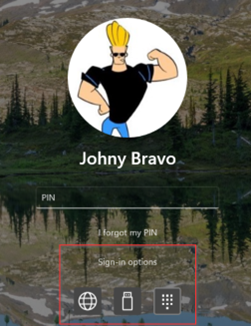
Before we are going to enable the passwordless experience feature, let’s first make sure that users can reset their PIN as a fallback. By default, this is not enabled in your tenant and would result in an error when hitting the ‘I forgot my PIN’ option, this as shown below. The error is mentioning the ‘lack of a service principal’, which is logical as you probably didn’t execute the required steps.

Before enabling the ‘Microsoft PIN Reset service’, it’s important to know that there are two types of PIN resets first (which are described here on the learn pages as well). We have destructive and non-destructive PIN resets.
For destructive PIN resets the Windows Hello for business container is deleted. This can be achieved by the following cmdlet ‘certutil.exe -deleteHelloContainer’. After the next sign-in to Windows 11 the user is re-prompted for Windows Hello for Business enrollment.
For non-destructive PIN resets the Windows Hello for Business contain is retained, however the PIN that the user used to authorize key usage is changed. Only for this challenge we need to enable the ‘Microsoft PIN reset service’ in Entra ID.
The first step is to enable the ‘Microsoft Pin Reset Service Production’. This can be done by going to this URL as a global administrator, application administrator or cloud application administrator within your tenant and hitting ‘Accept’ on the consent page to provide the ‘Microsoft PIN Reset Service Production’ application permissions to read data in your directory.
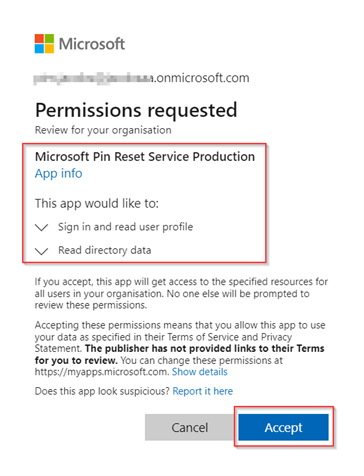
Once ready, let’s enable the ‘Microsoft Pin Reset Client Production’. This can be done by going to this URL as a global administrator, application administrator or cloud application administrator within your tenant and hitting ‘Accept’ on the first consent page to provide the ‘Microsoft PIN Reset Client Production’ application permissions to access the ‘Microsoft PIN Reset Service Production’ (which we added earlier) and sign-in and read data in your directory.

Once ready, let’s go to the Entra Admin portal, go to ‘Enterprise Applications’ and search for ‘PIN’. Verify that both applications are added successfully.

Once you’ve verified both applications are available within the ‘Enterprise Applications’ overview, let’s verify if Windows 11 has recognized you can reset your PIN. Therefore, sign-in to Windows 11, open a command prompt and run the cmdlet ‘dsregcmd.exe /status’. Beneath the ‘User State’ verify the ‘CanReset’ is reporting ‘DestructiveAndNonDestructive’.
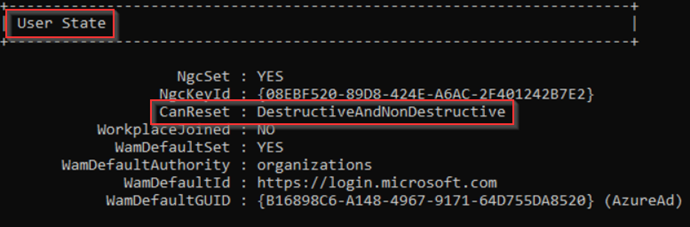
NOTE: In case that the ‘CanReset’ is only reporting ‘DestructiveOnly’ this either means your applications aren’t added correctly or the Windows Hello for Business PIN Recovery setting isn’t enabled on your device, to enable this for your device create a ‘Settings catalog’ policy within the Intune admin portal and make sure that ‘Enable Pin Recovery (User)’ is set to ‘True’ and make sure it’s assigned correctly.

Once the ‘CanReset’ state is reported correctly we can successfully make use of the ‘I forgot my PIN’ option without running into the error we’ve seen at the start.

Now the ‘Microsoft PIN Reset service’ is enabled in your tenant, let’s make sure to hide the password option in the login screen in Windows 11 and make sure that web sign-in is enabled as a fallback method next to PIN resets.
Step 2 – Create the policy for hiding the password option & enabling Web Sign-in
To enable the ‘Passwordless experience’ and ‘Web Sign-in’ feature for Windows 11, go to the Intune Admin portal, click on ‘Devices’, click on ‘Windows’ and hit ‘Configuration Profiles’.
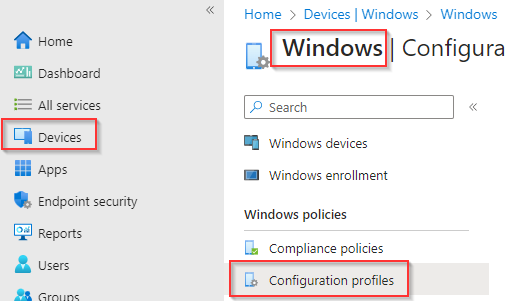
Now hit ‘+ Create Profile’, choose ‘Windows 10 or later’ and select ‘Settings Catalog’ and hit ‘Create’.
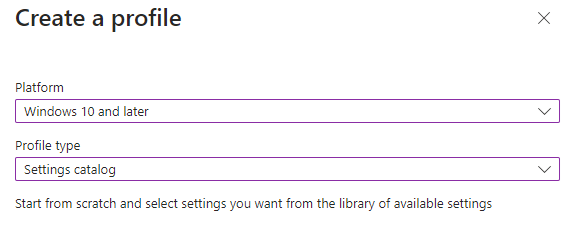
In the ‘Basics’ screen, give the Configuration Profile a ‘Name’ and ‘Description’.
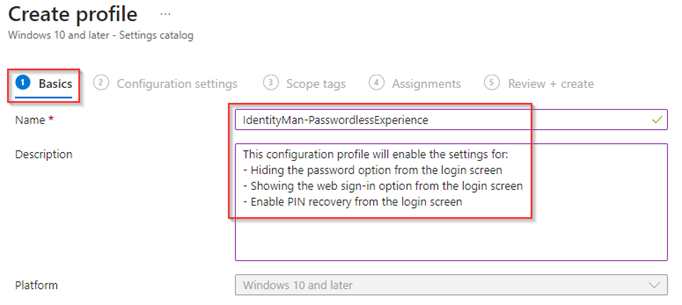
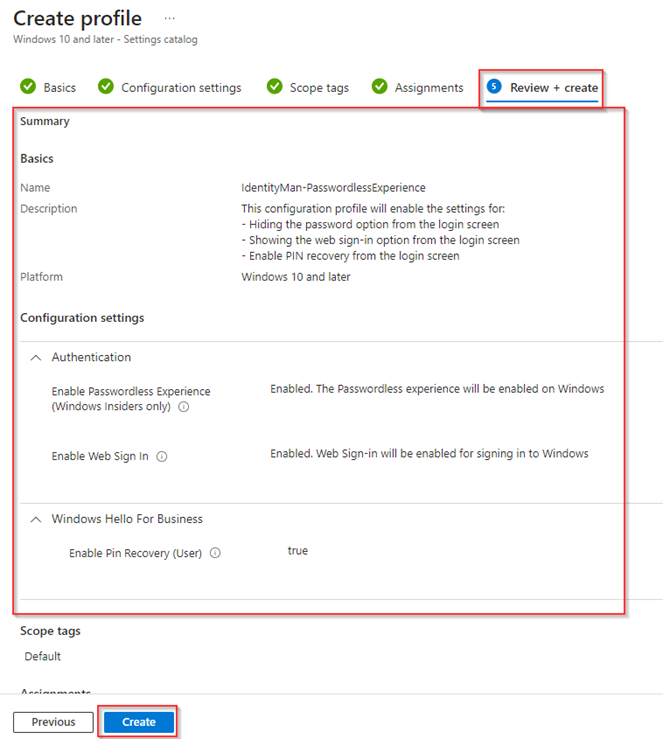
Within the ‘Configuration settings’ make sure to add the following settings:
- Enable Web Sign-in – Enabled.
- Enable Passwordless Experience – Enabled.
NOTE: As you can see, I’ve enabled the above two settings within the same policy as the ‘Use Cloud Trust For On Prem Auth’ feature as explained within one of my previous blogs.

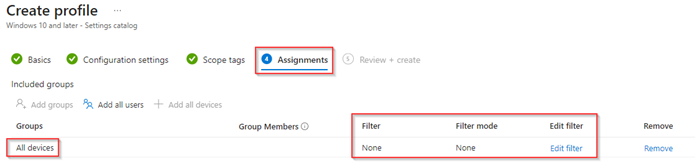
Eventually, if required, assign ‘Scope tags’ and make sure that in the ‘Assignments’ tab the configuration profile is targetted to devices. Why devices? This, as during the out-of-the-box experience you want to have the web sign-in feature enabled as soon as possible. So, when the device has an unexpected reboot or the user is presented with a lock screen (due to policies), the user can use web sign-in instead of the password option. In my example I’ve targetted the policy to ‘All devices’, but I can imagine you rather want to use something more specific. In my experience the best experience to achieve this is by using device filters (you don’t get this experience with dynamic groups as those can have an update delay and with that a delay in policy retrieval as well).
Next in the ‘Review + create’ overview, make sure the policy is configured correctly and once ready hit ‘Create’.
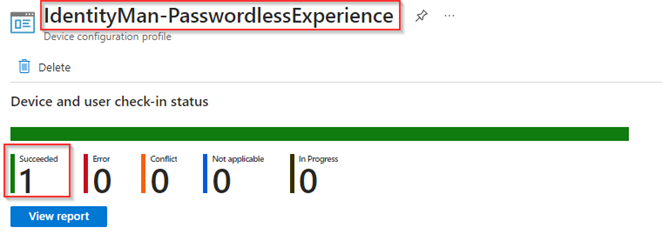
Now make sure to sync your device and verify the configuration profile has successfully applied on your device without errors.
Once all settings have landed on your device(s) and you’ve enabled the Microsoft PIN Reset service in your environment we are ready to verify the user experience, so let’s see what kind of magic we did enable.
Step 3 – Verify the end user experience
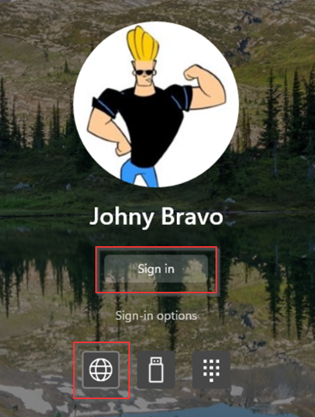
Now we have configured all the required components, let’s first checkout the new Passwordless Experience. As you can see from the sign-in or lock screen the password option is completely removed, which is just awesome!
If a user still wants or needs to sign-in with their password they can do that by clicking on ‘Other user’ and just type in their username and password.
Once we sign-in with for example the Windows Hello for Business PIN we see that if we go to ‘Settings’, hit ‘Accounts’ and select ‘Sign-in options’ we can see that the ‘Password’ option is not available anymore here as well.

And as mentioned at the start of this blog the ‘Run as different user’ option still has the ability to use a password as we didn’t removed the password credential provider.

With the above applied the ‘I forgot my PIN’ experience becomes extremely important, now with the PIN reset service being available in your tenant you can now simply recover from a PIN you’ve forgotten, this with even an improved experience.
And at last, the web sign-in experience we enabled is available (also during the out-of-the-box process as we assigned the policy to ‘All devices’). This will give your users a fallback option in case no other method is available to you.
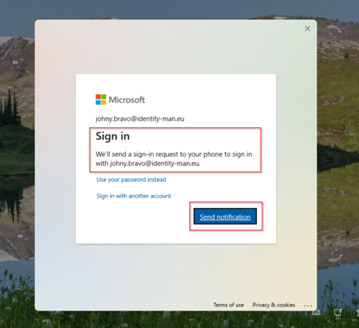
Hereby the user can for example make use of a Temporary Access Pass (or the Phone Sign-in method via the Authenticator app as shown below (which is not supported)). Important to mention here is that the Web Sign-in experience will hit your Conditional Access policies, and with that your configured Authentication Strenghts for a passwordless experience as explained in my previous blog post.
NOTE: Important here is that this method should not be used as a primary authentication method but only during bootstrapping your device or when you don’t have any other option, in most cases you will used this in combination with a Temporary Access Pass. This is mentioned here on the Microsoft learn pages as well.
Now we have seen the experience which we’ve created, let’s wrap up to the conclusion.
Conclusion
Now we’ve walked through the steps to enable PIN resets, made sure the configuration profiles are in place for the ‘Passwordless Experience’ & ‘Web Sign-in’ within Microsoft Intune. You should be fully ready to implement these features within your production environment and finally hide the password option from the login screen instead of just fully removing it from Windows 11.
It’s time to ban passwords from your environment (rather sooner than later) and with the ‘Enable Passwordless experience’ we can take a solid step into the right direction. All users who can use Windows Hello for Business from the Windows 11 Login Screen don’t need their password anymore so why should you still provide the option to use a password?
The ‘Enable Passwordless Experience’ feature, the improved ‘PIN reset’ and ‘Web sign-in’ experiences are released in Windows Insider build 23506 and will work in later builds as well. Let’s hope that Microsoft releases this functionality soon for the regular Windows 11 builds as well.
Now you know all of the above, let’s give you some last tips and tricks:
- First of course make sure you’re using a supported Windows 11 Insider build (Preview Build 23506)
- Always start with a small pilot group of users and devices, this to see the experience in production and know how people are going to respond to the password option being removed from the sign-in, lock screen and sign-in options.
- Create awareness about the web sign-in feature and don’t let people use this option for day-to-day sign-ins, web sign-in is a good fallback method and your users should be made aware of that.
- Web sign-in is only available for Entra Joined devices and is officially only supported with the use of a Temporary Access Pass.
- Authentication strengths are not applied during the Windows Sign-in, however when using Web Sign-in authentication strengths are applied.
- Later when the timing is right and passwords are not needed anymore in all scenarios on Windows 11 devices, you can decide to remove the password credential provider.
I again hope you enjoined reading this blog and are now ready to continue your passwordless journey with the new ‘Passwordless Experience’ feature. Let’s stay connected and stay tuned for more blogs in the going passwordless series in the future! :-).
Other related password-less blogs:
- Introduction to a password-less era
- Password-less 1 of 5: Going password-less with phone sign-in
- Password-less 2 of 5: Going password-less with Windows Hello for Business
- Password-less 3 of 5: Going password-less with Windows Hello for Business Hybrid
- Password-less 4 of 5: Going password-less with FIDO2 Security Keys Part 1
- Password-less 4 of 5: Going password-less with FIDO2 Security Keys Part 2
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 1
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 2
- Password-less 5 of 5: Expanding password-less to Azure AD Applications Part 3
- Password-less continued: Upgrading your password-less experience with Windows Hello for Business Hybrid cloud-trust
- Password-less continued: Using the Passwordless Phone Sign-in experience for multiple accounts on iOS!
- Password-less continued: Using a Temporary Access Pass for Bootstrapping your Passwordless Journey
- Password-less continued: Using Authentication Strengths to require Passwordless methods in your environment
- Password-less continued: Start hiding the password option from the login screen in Windows 11
Great article, very useful in what I’m trying to achieve!
Is disabling the ‘Other User’ option entirely a possibility, leaving only the web sign-in and FIDO options?
LikeLike
Not with this solution, for that you do need to remove the entire password credential provider.
LikeLike
I have the WIndows 11 Enterprise Insider Preview Build 23565 installed, but the Passwordless Experience and Web-SignIn didn’t work. Intune shows successful applied policies and on the client I could see that the Authentication polcy is applied..
I don’t see the Web-SignIn and the Password is available.. Do you have some tips?
LikeLike
Hi Marco, This was caused by a bug and has been fixed now (the same bug has been in non-preview builds as well and also fixed there).
LikeLike
This should also work for Hybrid-Joined Devices correct? I currently use Windows Hello For Business Hybrid-Cloud Trust & Microsoft appears to push this solution for Entra-Joined devices only. Thank you for this writeup.
LikeLike
Hi there,
The password hide option is only available for Entra joined devices indeed, this means Hybrid Entra Joined devices are not supported.
LikeLike
Hi,
I created a request in the feedback hub on Microsoft for this function, because we need this function too. We have a hybrid environment and at the moment it isn’t working.
If this function is available, it will be big step to a passwordless environemnt. May you can create a request too?
Regards,
Marco
LikeLike